Threat Assessment
Evaluate your organization's vulnerabilities and threats. Strike the right balance between risk management and operational efficiency.
"We hack your stuff, so you don't have to."
Enhancing Cybersecurity through proactive defense strategies of both Red and Blue Team, by simulating real-world cyberattacks, strengthening cloud security and mitigating potential threats.
RedTeam actively simulates cyberattacks, identifying vulnerabilities in systems and networks to enhance an organization's resilience against real-world threats. We're experienced in Pentesting and RedTeaming, including Defense Evasion, low-level Rootkit techniques, Social Engineering, AI & custom tools.
BlueTeam activities focus on fortifying defenses, detecting, and responding to cyber incidents, ensuring robust protection with IDS / IPS, DPI and quick recovery from potential breaches. Threat Hunting tools like osquery, Wazuh, Splunk or Elastic Stack, down to raw log file analysis, Digital Forensics and Incident Response (DFIR), including Malware Reversing are our daily business.

Cloud security ensures data and services in cloud environments are protected from emerging Cyber Risks. Cloud vendors provide top-tier security standards and tools, but at the cost of rising complexity, challenging architects to implement well-adjusted access management. Services include Cloud Pentesting and consulting on realistic vectors.
Our cybersecurity solution offers essential insight for assessing your systems and managing vulnerabilities. With straightforward reporting, you can identify areas for improvement and strengthen your overall security posture. We collaborate with you to ensure compliance with industry regulations, frameworks and standards, like the EU Cybersecurity Act, GDPR, NIS2, PCI DSS, HIPAA, ISO/IEC 27001, 27019, TIBER-EU/DE, BAFIN's MaRisk, Kritis IT Security Act, Energy Act and more. We actively contributed to DAX 500 internal security regulations and official, state-sponsored regulatory projects from BSI.

We hold certifications, such as OSCP, Malware Reversing, Security in Medical Institutions, Social Engineering and more.
Evaluate your organization's vulnerabilities and threats. Strike the right balance between risk management and operational efficiency.
Develop and refine your response strategies. Ensure preparedness while maintaining compliance and minimizing disruption.
Evaluate your existing security infrastructure and frameworks. Optimize effectiveness while ensuring operational efficiency.
Stay aligned with regulatory requirements and industry standards. Always be on time with security protocols and business operations.
Implement effective measures to safeguard sensitive information. Give user accessibility with robust security controls.
Establish ongoing surveillance of your security environment. Maintain vigilance while ensuring a seamless user experience.
Note that we keep client work strictly confidential, thus we can only show a piece of the whole picture, like generalized Lab reenactments of real hacking activity, tool & technique development and security research efforts.
Physical Attacks, Phishing Simulation, Info Stealer, C2 implants, Evasion... additionally to the bread & butter Active Directory Pentesting methods, like using CVEs, credential stuffing with CME and Metasploit or network-level tools such as Bettercap and Responder, we've been practising the real deal: We can create non-malicious malware and deliver a range of advanced attacks. Starting with intelligence, designing a long-term plan and finally executing stealthy attacks. We not only focus on technical details, but also on minimizing risk in accordance to regulatory frameworks like TIBER and reporting the things that matter to you. Making your company safer against Ransomware is not magic, but requires attention to detail and patience. We're happy to pwn you.
After over a year of work (pre-AI) and almost 2 years of runtime we had to take v1 offline, cause we could no longer afford running a big data server 24/7. We kept the frontend webserver though, in 2025 we managed to squeeze at least a light version of the most recent CommonCrawl dump into sqlite and directly on the Webserver, that now has it's 100Gb disk filled to the rim. But, it's pretty and fast now, we added some loadbalancing, yet the server is a 2-core turtle, so we beg forgiveness on one or the other timeout. If we ever get some financing together, we could provide the entire CC-goodness and truly become the only historic metadata search engine. Visit https://webhistory.info or check this list on our GitHub to see, what pearls are hiding in the CommonCrawl dataset:
We hold OSCP and a few smaller certs, made HTB rank Elite Hacker, pwncollege yellowbelt (inc. Yan85 solution of a fantasy-virtualisation-3-days-in-opcode-hell), Portswigger's WebSecurity Academy and a ton of training certifications - even though they're called training certs, many courses went in-depth on the specific topic and took up to 80h including lab excercises, multiple-choice questions with limited time, 1:1 similar to the actual certification exam. We couldn't afford each and everything we wanted to, instead we learned to find this stuff without any help and trained on more practical subject matter. More fun for us. Eventually we started to make our own little courses, but gave up soon, after realizing that we're terrible on camera. Current skill level: We're routined in finding the power-on button (after watching the Youtube tutorial again, that counts). Just, turning the damn thing off... Common, this stuff is hard. Why is it all new and different again?
We recently discovered this predecessor of Spiderfoot, recursive enumeration of Web targets, including email address, screenshots and more. It's so fast and deep that it killed our connection several times, a throttle option would be great (there's a slow mode but that will exclude some tools). Nevertheless, it's an amazing, modern tool for Redteam, BugBounty, OSINT and more. It comes as pip install and can easily be adapted into your own python scripts. As one of the countless features Bbot brings a standalone Dump Database, which it will search during scan automatically.
When trying this and similar UAC bypasses, it didn't want to work with CMD or Powershell as a value - because of Defender realtime scanning recognizing the registry change as malicous signature. Defender simply kills the entire process, meaning the Powershell we used to try the registry change. AMSI evasion is not sufficient as bypass. But using other values, like calc.exe, that didn't happen. So we tried next to get it working with WSL: Administrator.
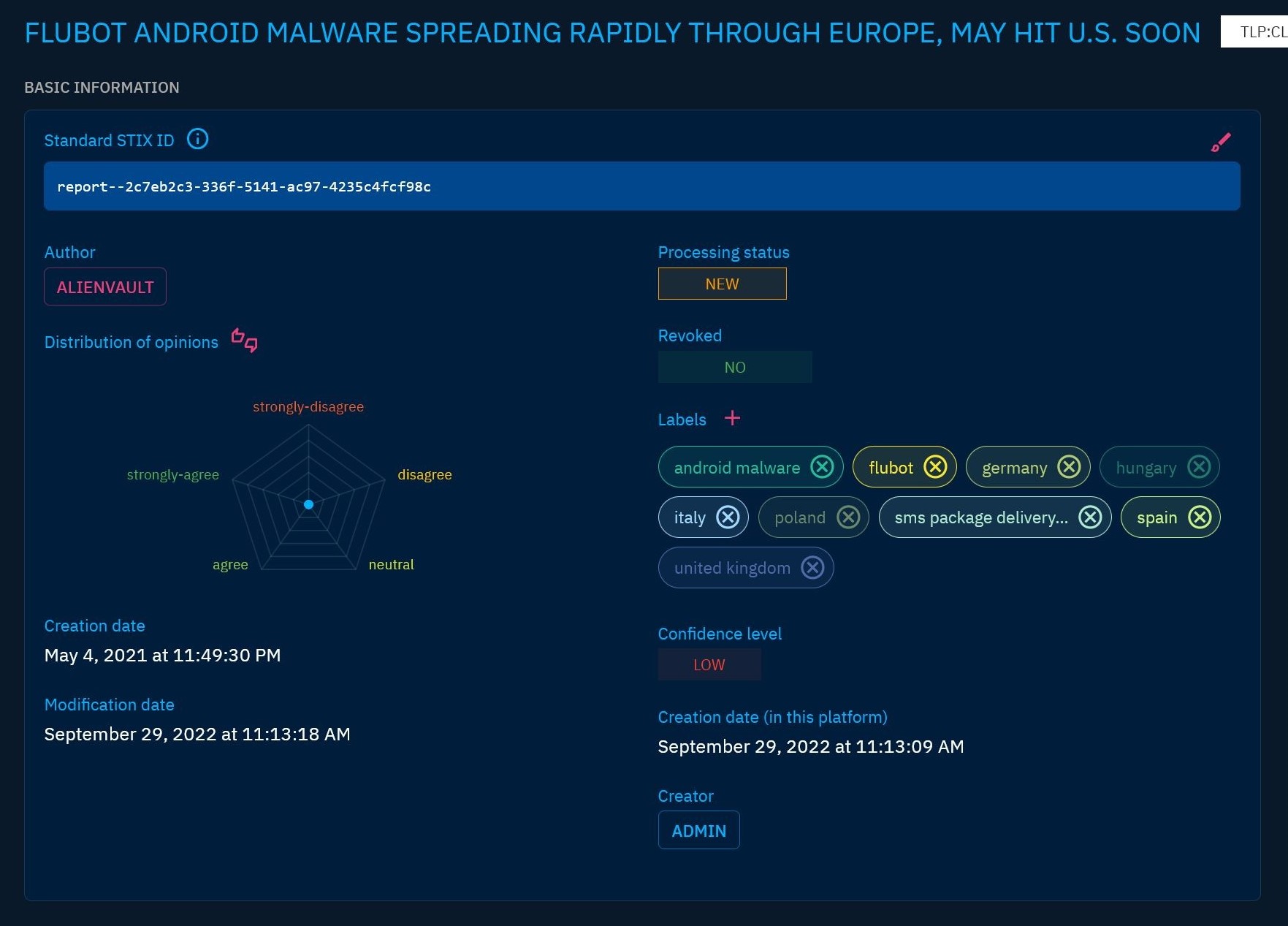
We setup, run and actively use many different SIEM solutions in our Lab. Especially Wazuh will have a place in our hearts for a long time, but also niche solutions like OpenCTI provide so much value, the only thing we miss, is enough disk space, cores and RAM for all the VMs. Portainer is a blessing for managing larger Docker stacks, at times we also use a local Kubernetes cluster. For better (or worse) times, we even have a separate server, so we can literally go on "DEFCON 1" - the term from the movies, not the conference - and surveille the crap out of every single device that ever touches our internal network and our webservers. Aside from these (and the PFSense we run always, including some onboard services like Snort, Suricata, Zeek, etc.) we make heavy use of the standard online stack, from AlienVault over Talos Intelligence to VirusTotal, only to name a few out of 10 platforms we use almost daily. We also gained experience with commercial solutions, like Splunk and a few more, while working for Companies and even though we don't use osquery & fleet actively, we did set it up a few times to get to know it.
In this example, we attacked our own, fully patched and updated AD (Server2019 / Win10), provided ourselfs an SSH shell to an AD client, where we also skipped PrivEsc and started as LocalAdmin (not that uncommon). Then we explored several pathes, like the Powershell 2.0 Evasion, which however had too many limitations to get really happy. So we switched over to Matt Graeber's First Reflection to evade AMSI, followed by disabling Real-Time Monitoring of Windows Defender, finally establishing persistance with our Sliver C2 implant and the undetected AnyDesk in a scheduled task (no screenshot, bit of a hazzle at first), also including evasion to get reboot-safe. Depending on Windows version and security settings, it may or may not work that easily, AnyDesk still is a safe bet even on high security systems - being able to conquer a modern AD, albeit it wasn't hardened it also didn't have any intentional misconfig - has been a dream we had for a long time. Again, it may not work that easily, we don't take it for granted and we're surely no AD experts. But we love doing it every time.
Threat Intelligence, that's done in our lab on a regular basis. Usually we're late to the party. Meaning, the phishing campain was already over, the attack would have no longer worked anyways, important building blocks, like a domain, already had been deleted from the global DNS. That's normal, campains run only between 12 and 48 hours. In this case, we followed the pieces that were left, tried Reverse Lookups and other OSINT techniques to see, if we could find anything. Yet, we're not LE, our capabilities end at a certain point. In many cases we can identify a person or group behind an IP, Email Address or other data: We tracked a Malware C2 to an infected University server in one case, or found a lowtech attacker and his social media pictures in Bangalore in another - but sometimes there's nothing, the attacker didn't use his private email for domain registration. To increase our investigative success rate, we made a script that can search an INBOX and automatically find SPAM, Scam, Phishing and alike, saves attachements and link URLs, so we can automate OSINT.
On a regular basis, we go out and hunt for new tools - SpiderFoot is absolute overkill when it comes to automated OSINT. That's not neccessarily a bad thing, though. While finding too much on a single person may equal finding nothing, using SpiderFoot in a Pentesting Scenario - while we conciously didn't add the mandatory "... and RedTeaming" here, cause that would focus on people OSINT again - it can give you quite amazing results, for literally just pressing a button and waiting 30min. Pro Tipp: Combine it with RAG, AI and Custom Search Engines like SearXNG. Truly powerfull!
When Binary Fuzzing gives you a cold shiver, thinking about complicated setups, followed by days of finetuning and then actually confirming the results, Radamsa is the quick & easy Fuzzer of your Pentest-Dreams. It's simplicity and easy of use makes it applicable in everyday Pentest scenarios: "Got an hour left, I'll run a quick Radamsa on this App before I finish...". Now you can truly claim, you're Fuzzing All The Things!
Using a custom, low-level implementation of the WinAPI function GetModuleHandle() we're able to read all DLL pointer reference addresses from the TEB / PEB, meaning all DLL libraries of a process. This is an essential function for Rootkit techniques like Privilege Escalations or Sideloading / Reflective Loading, that why advanced EDR systems monitor the call of such functions - our low-level implementation helps to evade this detection.
AI tools quickly became everyday companions for our work in Cybersecurity. GPT & friends happily write exploit code for us and help, to get all kinds of tasks done quicker, while free and opensource software like Fooocus and ComfyUI generate either cloned or fully artificial photos for Social Media profiles. AI can now replace malware reverse engineers with GhidraMCP, Ollama keeps the LLM-part local & GDPR-safe and although code-execution isn't their strong suit, a flood of custom tools along with ever-growing context windows made us all 10x unproductive (vibes away). In 2025 finally Audio became usable, imagine you'd have a voice matching all those names and numbers. And if you don't, cause they got no Youtube channel or TikTok... na, that doesn't happen anymore, cause: Keep your Zoom invite link close to your badge and both near your heart, meaning, onto X. Commit will follow. Realtime Video faceswap is no longer science fiction, everybody can do it from their gaming PC - that includes us. It's as funny as it is scary - if only we could act, like we would belong.
We tried to tackle the topic from a really wide angle, for several years we took a deep dive into Interrogation Techniques, classic Social Engineering (pretext & context), Human Fallacies, Negotiation tactics made known by Chris Voss, Deescalation, Psychology and not to forget: Competitive Business Intelligence (CBI) aka Dark Intel Techniques & Company Communication Tactics. Surely not all is applicable - or even needed - but it's definitely advantageous to know about it.
These days, we rarely even open up our dedicated Reverse Engineering and Binary Exploitation VM anymore, it would take us a few hours to get back on track with basic binary exploits, to be completely honest. Yet there's some tales we'll keep on telling, simply because their usefulness is right up there, probably Top 10. R2Ghidra is an installation procedure from hell, but if you make it, you'll no longer stare for hours into Assembly code, wondering what it might do and on which Stackframe you're currently on. Until you finally give up, open IDA or CutterRe, only to realize, you may have gained some insight, but at the price of moving from DAST to SAST and breaking your "bashing in single letter commands followed by cryptic Hex addresses" - flow. Having readable C-Code, Ghidra-quality, right in your GDB... you'll never go without it again!
BigData, Datalakes and OSINT are not only a regular part of RedTeaming and Security Research, they also are fascinating topics. In our BlackViz DB we can search over 500 Million records in less than 10ms, deliver thousands of results and display relationships in a Node graph, that offers unique insights and direct access to the detail records behind. All of this is done with simple tools, MongoDB, SQlite3, NodeJS, D3 and without 3rd Party search accelerators like Elastic. Recently we extended the features to visualize large-scale, company WiFi networks, sadly we cannot show the uncensored, beautiful results, that allow analysing network-level relationships.
Powershell in C# Runspace in Powershell. People just weren't prepared for our sense of humor. We're sorry. Not sure it actually worked though.
No longer up-to-date UAC Bybass we found quite fun. It may still work on stand-alone clients (including latest Windows 10). However, on most recent AD clients (tested against Windows Server 2019 and Win10) the issue has been patched, you need to confirm UAC to execute it there - despite the fact that rarely any systems currently in production use will be the latest version and configured securely - it's definitely worth knowing about, pretty interesting how some unconventional KIOSK-Escape style techique can work out in the end.
For couple of months we scanned S3 with a custom made spider. It's unbelievable, how many buckets are open to the world and contain sensitive data. Random Deep Web findings aside (fully aware public S3 search engines exist, that go far beyond our efforts), a good chunk of the buckets are publicly writeable. We left a warning and added them to our DB. On top, we used the scenario to test a little OpSec innovation we made. No spoilers. Finally we extended to Azure Blob, File, Queue, Table, Webapp and Vault Storage. We stopped somewhere in the range of 250k positive results, so no DB optimizations needed for our custom MisconfigStorage Search Engine.
One of these many, long nights OSINTing for nothing specific, a lead here, an idea there, we noticed that we don't have to go through the effort of making an entire Facebook account, just for stabbing a bit at the friends list of a target profile. Using only Firefox Dev Tools and bash, we saw that clicking around on a user's profile, like the gallery images, posts, background pic - anything that might have comments or likes on it - will generate GraphQL request and responses. When you filter and copy those out, clean it up a bit with some bash tools, you got yourself an improvised automation workflow to get, maybe not all, but most public infos of your target's facebook, without them having a chance to notice, who looked at their profile, and independent of the privacy settings of the target's friends.
Exploitation of csproj, sln and other Visual Studio project files to execute arbitrary code became famous with an attack on Security Researchers carried out by a state-sponsored APT. Lots of work has been done in this area since and many ways have been found to abuse these files, some are easy, some are complicated. We found 2 new easy ones.
To improve our security workflow, we use several SAST scanners. Automating the detection of vulnerabilities in code, scanning for many different vulns without effort. Simple yet effective tools to catch issues we might otherwise overlook, making it easier to focus our threat intelligence on what really matters.
Social Analyser is just one out of hundreds of tools and services we use for Open Source Intelligence (OSINT). We refined our skillset in finding information on technology, hacking tools, data and people for many years, today we're routined in analysing information and producing actual, actionable intelligence. Usually that takes only a few minutes. We play Geodetective in our spare time, even though we couldn't compete with pro players, the gained experience is more than enough for our daily work, furthermore we discovered Google Earth VR not only as professional tool, but also as a way to travel the world virtually. We never do HUMINT, we hardly ever touch a target's website directly anymore, most of the times we don't need to. As privacy advocates, we don't invade other people's private space and would hope, that this respect could be mutual.
The fun never stops.